IS
Size: a a a
2019 February 06
Ситуация очень интересная. Как я понимаю у разрабов и комьюнити есть стремление в будущем полностью избавиться от прозрачных адресов, т.к. прозрачные адреса это полностью подрывают идею анонимности. А тут они используют прозрачные адреса, чтобы убедиться не был ли проэксплуатирован баг. Похоже что такая сложная система не может быть надежной. Я думаю на этой новости в мире прибавилось биткойн максималистов)
DK
Баланс прозрачных адресов не даёт никаких гарантий неиспользуемости бага
DK
Ну и возможность существования такого бага была очевидна всем ещё 4 года назад, когда zerocoin только предложили
DK
Ну и статьи надо получше аудировать, хотя это тоже не панацея
IS
Баланс прозрачных адресов не даёт никаких гарантий неиспользуемости бага
При миграции на сеплинг вроде как надо перевести деньги сначала на прозрачный адрес. И таким образом мы увидим сколько денег было выведено с шилдед адресов. И таким образом будет понятно был ли проэсплуатирован баг.
N
При миграции на сеплинг вроде как надо перевести деньги сначала на прозрачный адрес. И таким образом мы увидим сколько денег было выведено с шилдед адресов. И таким образом будет понятно был ли проэсплуатирован баг.
Вот так анонимность
DK
При миграции на сеплинг вроде как надо перевести деньги сначала на прозрачный адрес. И таким образом мы увидим сколько денег было выведено с шилдед адресов. И таким образом будет понятно был ли проэсплуатирован баг.
Правда что ли? Можете ткнуть пальцем?
DK
А, ну это типа опционально
IS
А, ну это типа опционально
Пока да, но через пару лет, они могут прекратить поддержку старых адресов.
DK
Это было бы глупо
DK
Скорее уж биржи перестанут поддерживать
IS
биржи и так не поддерживают шилдед адреса, только прозрачные
DK
Ну тогда да, может и прикроют. Софт форка должно хватить
DK
Ну и статьи надо получше аудировать, хотя это тоже не панацея
Я бы еще добавил, что генерация всех этих ключей в результате сложной церемонии сделала быстрый фикс практически невозможным.
DK
Ну у них тот же сетап как я понял
2019 February 07
DK
Вот моё summary по zcash
DK
ZcashGate
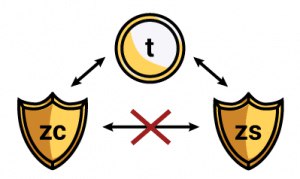
Today the Zcash team announced a major vulnerability found and fixed in the Zcash protocol. https://z.cash/blog/zcash-counterfeiting-vulnerability-successfully-remediated/
The story is quite controversial: the flaw was deemed too complicated to discover by attackers but extremely exploitable under a smallest hint. Because of that the fix was covertly added to the upcoming hard fork, Sapling, 8 months after its discovery.
The details are as follows. The zkSNARK technique requires a trusted party to generate the key pair needed for proof construction and verification. The key generation requires a secret, which should be kept secret by the trusted party or generated collectively by a group of participants ("trusted setup ceremony"), because the one who knows the secret can generate fake proofs.
The original Zcash was based on the 2014 paper by Ben-Sasson et al., which was itself a modification of the 2013 paper by Parno et al. The newer paper introduced a faster proof technique, which required publishing a few more secret-dependent polynomials during the setup phase. The 2014 paper did not prove the necessity of all these polynomials (the 2013 one did for its own set). In 2015, before the Zcash launch, Parno found a flaw in the 2014 paper, showing that these polynomials contain an excessive information about the secret used by the trusted party and thus allowing easy fake proof generation. The revised setup still did not come with a proof of correctness.
Apparently this was not the only bug to be found in that setup. In March 2018 Gabizon discovered another bug of the same kind. The problem was that the trusted setup for Zcash has already happened and anyone who would find this bug could print ZEC coins out of air. Given the alternative of stopping the entire Zcash protocol, the small subteam of Zcash decided to keep it secret till the next trusted setup, which eventually happened in October 2018 and was based on a different 2016 paper by Groth, now with a security proof.
Gabizon has since found the proof of correctness for the revised 2014 paper, but it was too late. https://github.com/arielgabizon/bctv/blob/master/bctv.pdf?fbclid=IwAR1wKtN8Ddh9IDuhIqd2O55MKQQG1z5tJB_t-X6ZgXYIPKzhbjSsIRCGv7o
This story demonstrates that the trusted setup ceremony, due to its complicacy, is error-prone and is very difficult to fix. I also lost confidence (a bit) in Zcash, as we do not know if they have already found a bug after the second ceremony and wait for the third one. I doubt the judgement that no one else could have found the bug. I think that even though a cryptographer was needed for that, the place to search was very clear: it is a lemma without a proof.
Let us see how it goes.
Today the Zcash team announced a major vulnerability found and fixed in the Zcash protocol. https://z.cash/blog/zcash-counterfeiting-vulnerability-successfully-remediated/
The story is quite controversial: the flaw was deemed too complicated to discover by attackers but extremely exploitable under a smallest hint. Because of that the fix was covertly added to the upcoming hard fork, Sapling, 8 months after its discovery.
The details are as follows. The zkSNARK technique requires a trusted party to generate the key pair needed for proof construction and verification. The key generation requires a secret, which should be kept secret by the trusted party or generated collectively by a group of participants ("trusted setup ceremony"), because the one who knows the secret can generate fake proofs.
The original Zcash was based on the 2014 paper by Ben-Sasson et al., which was itself a modification of the 2013 paper by Parno et al. The newer paper introduced a faster proof technique, which required publishing a few more secret-dependent polynomials during the setup phase. The 2014 paper did not prove the necessity of all these polynomials (the 2013 one did for its own set). In 2015, before the Zcash launch, Parno found a flaw in the 2014 paper, showing that these polynomials contain an excessive information about the secret used by the trusted party and thus allowing easy fake proof generation. The revised setup still did not come with a proof of correctness.
Apparently this was not the only bug to be found in that setup. In March 2018 Gabizon discovered another bug of the same kind. The problem was that the trusted setup for Zcash has already happened and anyone who would find this bug could print ZEC coins out of air. Given the alternative of stopping the entire Zcash protocol, the small subteam of Zcash decided to keep it secret till the next trusted setup, which eventually happened in October 2018 and was based on a different 2016 paper by Groth, now with a security proof.
Gabizon has since found the proof of correctness for the revised 2014 paper, but it was too late. https://github.com/arielgabizon/bctv/blob/master/bctv.pdf?fbclid=IwAR1wKtN8Ddh9IDuhIqd2O55MKQQG1z5tJB_t-X6ZgXYIPKzhbjSsIRCGv7o
This story demonstrates that the trusted setup ceremony, due to its complicacy, is error-prone and is very difficult to fix. I also lost confidence (a bit) in Zcash, as we do not know if they have already found a bug after the second ceremony and wait for the third one. I doubt the judgement that no one else could have found the bug. I think that even though a cryptographer was needed for that, the place to search was very clear: it is a lemma without a proof.
Let us see how it goes.